What Is Access Request and How Do You Manage It?
Learn how you can implement an access request policy process to protect your business from data breaches and security compromises


Organizations must be thoughtful when providing access to internal systems. Security breaches can have a disastrous impact on an organization's brand, not to mention the damage exposed customer data can have on an individual's financial and personal life. There are best practices that should be followed that will help you ensure the security of your company data. An access request management policy can help.
In this article, we'll learn what access request is all about. We'll get a glimpse at how you can manage access requests and the tools available for this task. Additionally, we'll discuss some of the best practices to help you ensure that your access request policies protect you and your customers from a breach.
What Is Access Request?
An access request is a formal process that dictates how an individual can gain entry to a specific system or piece of information. IT organizations are bound by privacy laws to protect the data they manage and generate. Sometimes, this information is required to improve the overall services rendered by the company. For instance, the company's employees or third-party service providers may require this information. An individual must make a formal request to gain access.
"An access request is a formal process that dictates how an individual can gain entry to a specific system or piece of information."
Importance of Access Request
When teams make access requests a top priority, handling data becomes safer. For instance, teams can prevent data compliance risks and threats from data breaches. Here are some important benefits provided by utilizing access requests:
- Mitigating Internal Threats: An employer can not ensure that all employees are guided by an ethical or moral set of codes. Some employees might use sensitive data for nefarious purposes. More often, an employee might make an accidental mistake that allows data to be breached. Access requests helps the organization easily trace who has access to data which can help prevent a breach.
- Reducing Online Attacks and Data Leaks: Implementing access requests in your company helps reduce the possibility of successful online attacks and data leaks by protecting your data with security and controls.
- Preventing Malware Attacks: Access request policies help ensure a proper audit trail. For example, when using an access request policy, the record of the request helps ensure that offboarded employees have returned hardware and software accounts have been deactivated, which can help prevent a malware attack. Not knowing who has or once had access creates a blind spot.
What Is Access Request Management?
Access request management covers every process that leads to the actual approval or rejection of an access request. It's a set of processes ranging from receiving the access request to evaluating the request. In most organizations, the access request manager is the person evaluating such a request. This IT expert will prepare the methods of how the requests are to be sent and cross-check each request against the company's data policies, at which point they'll approve or deny the request.
"Access request management covers every process that leads to the actual approval or rejection of an access request."
The request manager is pivotal to the company's success. Their job goes beyond just acknowledging a request or identifying the requester—they ensure the security and efficiency of the company's operations. They analyze each request by critically looking for risks and threats hidden within such a request, irrespective of who the requester is, a trusted employee, or a third party.

Best Practices for Managing Access Requests
An organization that wants to excel at safely and efficiently managing access requests should apply some of the practices listed below. These methodologies make the daunting task of access request management manageable.
Develop Organization Access Policies
Every organization should have policies on how access to data is granted. This will act as a guide for who is permitted access to what information. If implemented correctly, order and security will be a top priority in the organization, and employees won't be able to access data beyond their clearance level.
Design Request Templates
Access request managers should develop a template by which access requests are made. The template design should reflect the organization's unique needs and data policies. This will help enforce a consistent process and make assessments and evaluations of requests easier.
Conduct Periodic Access Reviews
Always conduct periodic reviews on your access authorizations. Proper reviews will enable your organization to ascertain who has access to data. Furthermore, it helps maintain the security of your data. An access request manager should conduct reviews regularly, which can be done manually or through automation.
Manage Duration of Access
Giving access to resources a duration-based limit is a great practice, assigning an appropriate timeframe for how long someone can access the data. This is a security check operation. If the requester's time lapses, they must request access again.
Automate the Process
Automation of requesting access and managing access requests has proven very beneficial for organizations. It helps enforce the organization's access policies and data compliance expectations. Automation also makes the access request process easier through self-service options. At the heart of automating access request management is a ticketing system, which helps put every request in order of priority based on importance and other attributes. The first step toward great automation is selecting the right tools and solutions.

Automating Access Request Management
Now, more than ever, brands must ensure data leaks are prevented. Once a leak has occurred, controlling the legal and public relations ramifications can be difficult. An investment in an access request management process could save incalculable brand capital for a business. Automation provides a high ROI by reducing manual labor and helping prevent human error.
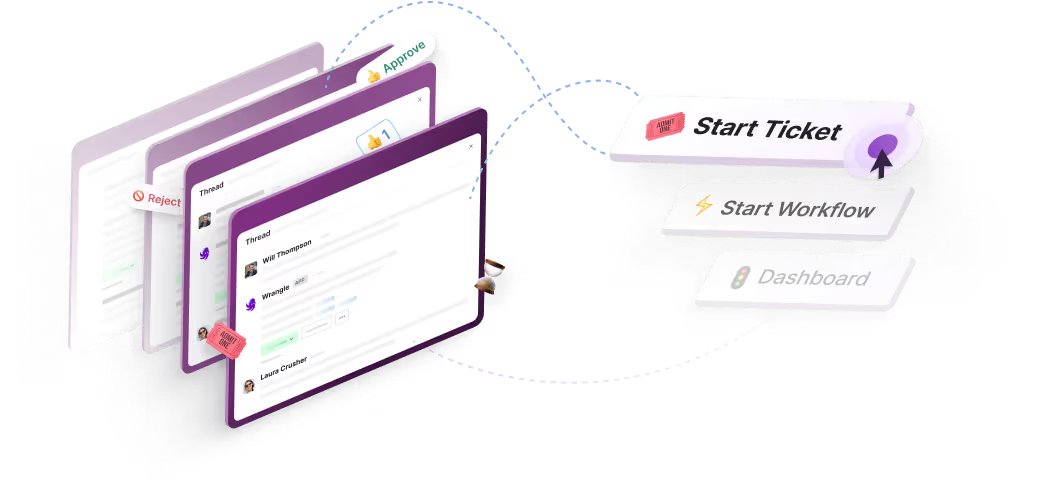
As companies move from email to Slack, many IT managers look to Wrangle as an access request management system. Wrangle is a ticketing and workflow application that lives in your Slack workspace. User agents can use Wrangle’s ticketing or workflow functionality to manage access requests in their business effectively.
Requesters simply visit a Slack channel to create a ticket or choose a workflow that suits their needs. Here’s how to use Wrangle to manage access request management in your organization.
First, let’s add Wrangle to your Slack workspace. Simply click the Add to Slack button on Wrangle’s homepage and continue through the installation process.

You could handle an IT access request through a Wrangle ticketing inbox or a workflow. Tickets are excellent for one-off requests. Users can simply ask a question in a Slack channel, and the prompt creates a ticket that an agent claims. It’s easy and efficient. But in this case, we might want a more automated process, so let’s use a Wrangle workflow.

Wrangle has templates for many business processes. In fact, there is a template for IT access requests, and IT change management. We’ll choose access management.

Wrangle will ask us to assign agents to the tasks in the template. The agents are your Wrangle users. For access requests, these are generally members of the IT team. Note that your end user, those requesting access, won’t need a Wrangle account. They’ll be able to make requests in the Slack channel.
Our template has three steps. The first step is the intake form, which your users will see in Slack. We have several fields they’ll need to fill out when they’re requesting access to a system. You can add or subtract any field based on your organizational needs. Of course, all of this is editable.

The second step is when the agent approves the access request. When an employee has asked for access via the intake form, the workflow will send the request to the agent assigned in the approval step. She will have all the information she needs to make a decision about the request based on the context in the intake form. When the approval request is made, it will be posted in the Slack channel we select. We’ll also keep the user informed of the progress of the request throughout the lifecycle of the IT access request workflow.

Once the agent has reviewed and approved, the workflow will move onto the Task list. In this case, it’s a simple set of tasks: provision access to the requested system. The agent will get an alert in Slack informing them that they may provision and move on to their next work set.

We now have an IT access management workflow process in our company Slack channel. Employees with access to the workflow can easily kick off an IT access request by typing /wrangle anywhere in Slack or going to the Wrangle app in their Slack dashboard.

Once the workflow is started, the requester will fill out the information we require in our intake form. In this example, our employee Lucas will request access to GSuite.

Once Lucas submits his request, the workflow will ping his manager Beverly for approval. If Beverly is unavailable to approve access, she can re-assign this request to another team member. She could also send the request back to Lucas for more information. Wrangle will post an alert in the Slack channel so other members can see the request, helping maintain a transparent work environment.

When Beverly approves the access request, the workflow will proceed to the provisioning stage.

Once the task list is completed and the access request granted, Lucas is alerted that he now has access to GSuite.

Conclusion
A solid access request management process can help ensure security, order, and discipline within your organization. Proper access request management minimizes the risk of data compliance failures or breaches. Let Wrangle help you implement an effective access request process. Request a demo of Wrangle or add it to your Slack workspace for a free trial.
Bertram Nnalue wrote this post. Bertram is a Python developer, data analyst, DevOps engineer, and a blockchain enthusiast. He is passionate about sharing knowledge and is dedicated to lifelong learning.
Wrangle learns from your tickets and knowledge base to handleup to 75% of Slack questions automatically.

4.7 Average rating




Turn Slack into a productivity powerhouse with Wrangle
Create a scalable helpdesk in Slack. Automatically turn messages into trackable tickets and provide faster, more transparent service to your colleagues and customers with Wrangle — Try it free!


.svg)




